
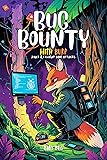
Bug Bounty with Burp: PART 2 – Client-side Attacks for Ethical Hackers and Web Pentesters
Format:
Kindle
Kindle
Paperback
Sin stock
0.20 kg
No
Nuevo
Amazon
USA
- Bug Bounty With Burp: Part 2 – Client-side Attacks for Ethical Hackers and Web PentestersReady to hunt where others fear to look? Master advanced client-side hacking using Burp Suite — no fluff, just sophisticated attack chains.This advanced cybersecurity guide is designed for experienced bug hunters, ethical hackers, and penetration testers ready to dominate the client-side attack surface. You'll master complex vulnerabilities that bypass modern protections using the industry-standard tool: Burp Suite.🚫 No basic tutorials 🚫 No outdated payloads ✅ Just advanced exploitation techniques, automation workflows, and attack chaining methods used by elite researchers.🔍 What You'll Master:How to exploit advanced XSS contexts that bypass CSP and framework protectionsHow to execute DOM manipulation attacks including clobbering and prototype pollutionHow to chain CORS misconfigurations with authentication bypass for data exfiltrationHow to hijack WebSocket connections for persistent, real-time attack scenariosHow to automate discovery with custom Burp extensions and advanced workflowsHow to build sophisticated attack chains that turn medium bugs into critical findingsBuilt around 60+ hands-on labs, this book assumes you've mastered server-side basics and are ready for the next level of web application security testing.🔑 Key Features:Advanced client-side vulnerability exploitationProfessional attack chaining methodologiesCustom Burp Suite automation techniquesReal-world bug bounty scenariosPerfect for experienced hunters seeking edge techniques📚 Part of the Definitive Bug Bounty Series This is Book 2 of the comprehensive journey.If you've ever wondered: "How do I find bugs that automated scanners miss?" "What separates professional researchers from script kiddies?" "How do I chain vulnerabilities for maximum impact?" ...this book is your arsenal.Ready to hunt at the next level? Every advanced bug starts with deeper thinking. Let's break things beautifully.
Producto prohibido
Este producto no está disponible
Otros Productos
Ver másCompra protegida
Disfruta de una experiencia de compra segura y confiable
¿Cómo comprar?
Información de Aduanas Ecuador
En Tiendamia puedes hacer tus compras a través de la categoría B (4x4) y la categoría C. No tendrás que hacer trámites de aduana. Hacemos todo por ti.
- El 4x4 (o categoría B)
- a. No paga impuestos ecuatorianos.
- b. Tienes una cantidad ilimitada de órdenes en el régimen 4x4 siempre que cada una de estas esté dentro del peso máximo permitido (hasta 4 kg) y no superen los $400, además de cumplir con el cupo anual por persona.
- c. El cupo anual máximo es de $1.600 al año para compras en el exterior a través del régimen 4x4. El cupo anual se limitan a una cédula pero no a tu usuario de Tiendamia.
- d. Se puede comprar una gran variedad de productos dentro de esta categoría siempre y cuando cumplan con el 4x4 y no sean para fines comerciales, por esa razón, se puede comprar máximo 3 productos iguales o similares de la misma categoría. Por ejemplo, puedes comprar hasta 3 perfumes, hasta 3 relojes y hasta 3 pares de zapatos, si te excedes de esta cantidad tu orden puede tener cargos extra por parte de la aduana.
- Las tablets, laptops y celulares se pueden comprar a través de la Categoría C.
- a. Esta categoría sí paga impuestos (IVA + Fodinfa)
- b. Solo se puede comprar un celular nuevo al año, no se admiten refabricados, usados u “open box.”
![]() Garantía de entrega
Garantía de entrega
Con Tiendamia todas tus compras cuentan con Garantía de Entrega o devolución total de tu dinero.
Compras 100% seguras y garantizadas, para que pidas lo que sueñas y lo recibas del mundo a tu puerta.
¿Cómo solicitar una devolución?
Para solicitar una devolución, el cliente debe realizarlo a través de su cuenta de Tiendamia. Este proceso está sujeto a la aprobación del departamento de Devoluciones (lo cual puede demorar de 48hs a 72hs hábiles). En caso de no tener la opción en la web, el cliente debe contactarse con Atención al Cliente para iniciar la solicitud.
Los productos sin devolución son:
- Los productos que tienen un tiempo de entrega mayor a 20 días hábiles.
- Productos que por su naturaleza no admiten devolución en EE.UU. o China y, por lo tanto, Tiendamia no puede ofrecer la devolución al cliente. Ejemplos: perfumes, cremas y medicamentos.
Tarjetas de Débito y Crédito

Visa

Mastercard

American Express

Dinners

Discover

Alias
Pagos a través de PayPal
Compra procesada en dólares con dinero en cuenta o tarjetas internacionales.

PayPal















.svg)
