
Bash for Black Hats: Offensive Shell Scripting Techniques for Hackers, Red Teams, and Security Professionals
Format:
Paperback
En stock
0.70 kg
Sí
Nuevo
Amazon
USA
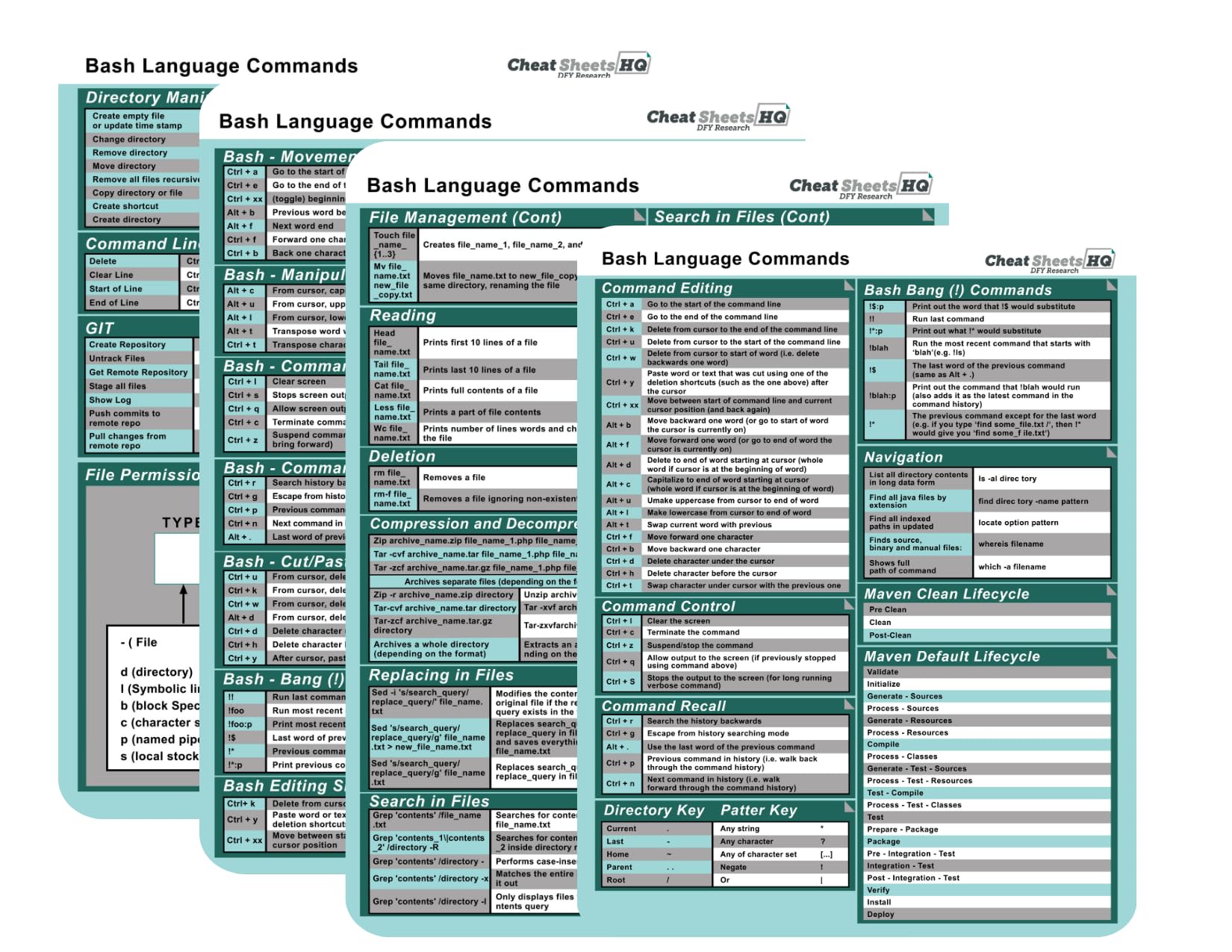
- Take your offensive security skills to the next level with this hands-on guide to writing powerful, stealthy, and effective shell scripts. Bash for Black Hats is not just a scripting reference—it’s a complete operational toolkit for real-world red teamers, ethical hackers, and advanced penetration testers who want to weaponize Bash in post-exploitation, persistence, evasion, and lateral movement scenarios. Written by a seasoned offensive security expert with deep field experience in red teaming, this book brings you field-tested tactics backed by solid technical explanations and practical walkthroughs. Whether you’re performing covert operations in complex Linux environments or automating attacks at scale, you’ll find proven methods that work in real-world scenarios—not just labs. About the Technology: Bash is still one of the most powerful and widely available shells in Unix-based systems. Its scripting capabilities can be weaponized for reconnaissance, privilege escalation, persistence, credential access, and beyond. With no need for third-party binaries, Bash is the silent backbone of many attack chains—simple, flexible, and trusted by the system. What’s Inside:Automating reconnaissance with wrappers around nmap, ldapsearch, and enum4linuxReal-world post-exploitation workflows scripted in pure BashAdvanced persistence using fileless techniques and cron jobsLateral movement with SSH, SCP, and harvested credentialsScripted privilege escalation checks and custom payload obfuscationAnti-forensics, stealth logging, shell history manipulation, and log tamperingToolkit modularization, background threading, and execution controlFinal cleanup, secure artifact removal, and OPSEC scripting tipsAppendices with payload templates, command cheatsheets, and field glossaries Who This Book Is For: This book is designed for penetration testers, red team operators, ethical hackers, bug bounty hunters, CTF participants, and system attackers who already understand Linux basics and want to develop deeper, low-level offensive capabilities. It's not for complete beginners—you’ll get the most value if you're already familiar with command-line environments and want to sharpen your edge. Security environments evolve fast—and so do defenses. If you're relying on outdated tools or GUI-heavy frameworks, you’re already behind. Bash gives you direct, scriptable access to the system's heart. The sooner you master it, the more control you gain over your operations—and your adversary’s infrastructure. This isn’t just another Linux book—it’s a highly tactical, code-rich manual filled with reusable scripts, modular functions, and strategic insights drawn from real red team operations. You’re not just learning Bash. You’re turning it into a weapon. If you're serious about building reliable, stealthy, and effective attack scripts, grab this book today and start weaponizing your Bash skills like a professional. Don’t just learn how Bash works—use it to take control.
IMPORT EASILY
By purchasing this product you can deduct VAT with your RUT number



























.svg)
